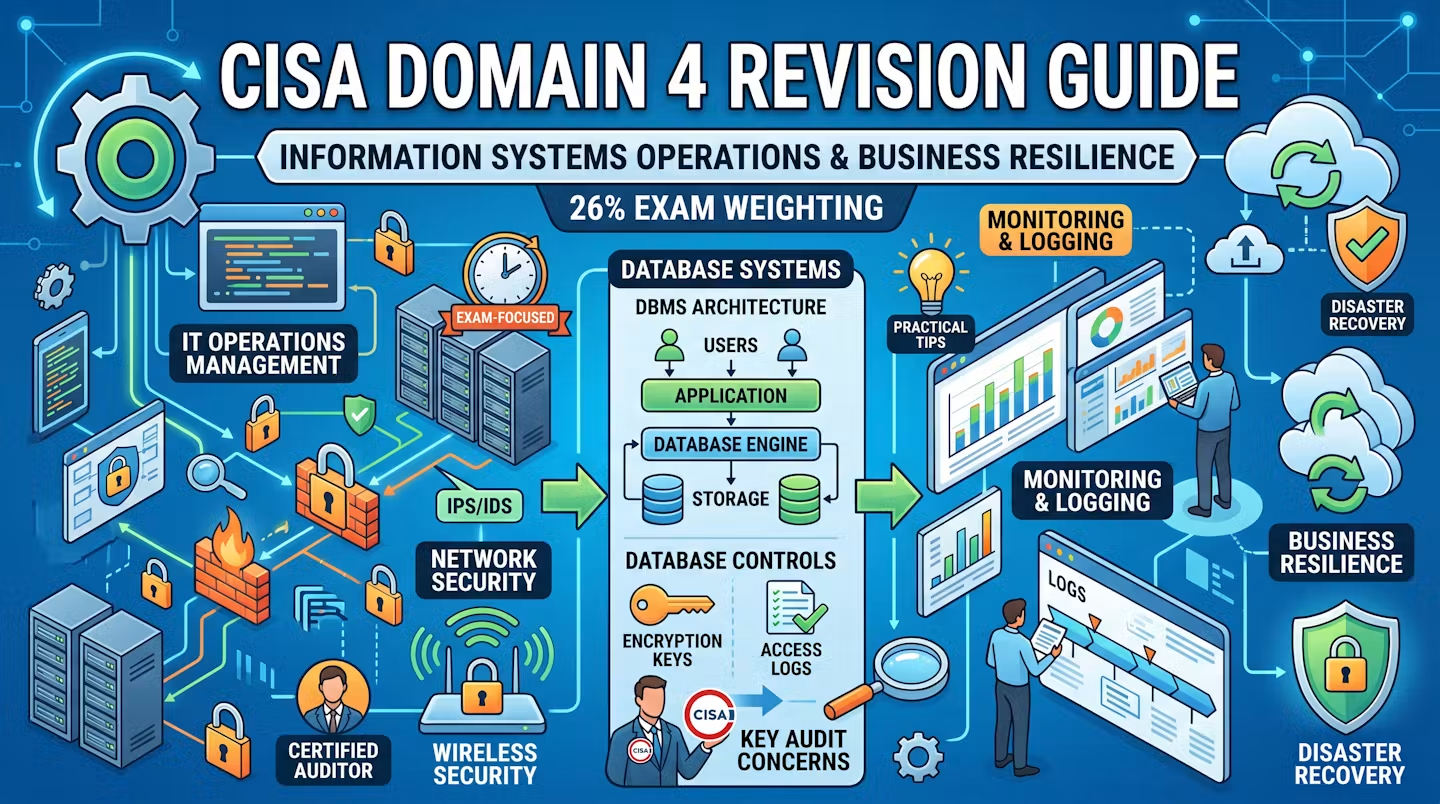
Essential CISA Domain 4 Revision Guide: Proven Exam Tips for Success
This CISA Domain 4 revision guide explains IT operations management, network security, wireless security, DBMS architecture, database controls, and monitoring and logging in an exam-focused way. You will learn the key audit concerns, high-value comparisons, and practical exam tips needed to answer scenario-based CISA questions.