Introduction
This CISA Domain 4 revision guide explains IT operations management, network security, wireless security, DBMS architecture, database controls, and monitoring and logging in an exam-focused way. You will learn the key audit concerns, high-value comparisons, and practical exam tips needed to answer scenario-based CISA questions.
Domain 4 is officially titled Information Systems Operations & Business Resilience and is currently weighted at 26% in the ISACA exam content outline.
Use these CISA Domain 4 study notes to revise faster, understand controls clearly, and strengthen your preparation for the CISA exam
IT Operations Management
Include: job scheduling, system monitoring, incident handling, backup execution, SOPs, runbooks, segregation of duties, and shadow IT.
“IT operations management” refers to the day-to-day execution and control of IT services to ensure systems run reliably, securely, and efficiently. Poorly controlled operations lead to outages, data corruption, and audit findings.
Shadow IT refers to unauthorized applications or services operating outside formal IT governance. Corporate IT is governed, monitored, and secured, while shadow IT lacks visibility and control, leading to risks such as data leakage, compliance violations, and weak access control.
Key Areas
- Job scheduling (batch/manual/automated)
- System monitoring
- Incident handling
- Backup execution
Controls
- SOPs and runbooks: without them, operations become dependent on individuals rather than processes, increasing risk.
- Segregation of duties (SoD) – Prevents conflicts of interest. For example, a developer should not directly deploy code into production because it bypasses independent validation
Network Operations Management
Include: network monitoring, availability, redundancy, failover, load balancing, network documentation, and configuration management.
Network operations focus on the day-to-day functioning, monitoring, and maintenance of network infrastructure (LAN, WAN, internet connectivity).
Key Components
Network Monitoring
Continuous observation of network devices (routers, switches, firewalls) to ensure availability and performance. Monitoring tools track the following:
-
- Bandwidth usage
- Latency
- Packet loss
Concept: Monitoring is a detective control—it identifies issues but doesn’t prevent them.
Network Availability
Ensuring that network services are accessible when required.
- Achieved through:
- Redundancy (multiple links)
- Failover mechanisms
- Load balancing
Exam Insight:
If availability is critical, redundancy is always the best answer.
Network Documentation
Includes network diagrams, IP schemes, and configurations. Without documentation: Troubleshooting becomes slow and Recovery becomes unreliable
Configuration Management (Network Devices)
Ensures routers/switches/firewalls are configured securely and consistently. Important considerations should be: Backup of configurations, Version control, Change tracking
Risk: Unauthorized configuration changes can disrupt entire networks.
Audit Focus
- Are network devices monitored in real-time?
- Are configurations backed up and controlled?
- Is there redundancy for critical links?
Network Security Controls for CISA Domain 4
Include: firewalls, IDS vs IPS, network segmentation, encryption, firewall rule review, and sensitive traffic encryption.
Protection of network infrastructure and data from unauthorized access, misuse, or attacks.
Key Controls Explained
Firewalls: Act as a barrier between trusted and untrusted networks. Key concepts include: Rule-based traffic filtering, following least privilege principle etc.
Exam Trap:
“Allow all, then block specific” is weaker than “deny all, then allow specific.”
Intrusion Detection vs Intrusion Prevention
IDS (Intrusion Detection System): Detects suspicious activity, generates alerts
IPS (Intrusion Prevention System): Detects and blocks malicious activity
Key Difference: IDS = Detective, IPS = Preventive
Network Segmentation
Dividing networks into smaller zones results in limiting spread of attacks and protection of sensitive systems
Example: DMZ for public-facing servers
Encryption
Protects data in transit. Protocols like SSL/TLS, VPNs. Encryption ensures confidentiality, not availability.
Audit Focus
- Are firewall rules reviewed regularly?
- Is sensitive traffic encrypted?
- Are IDS/IPS systems monitored?
Wireless Networks and Security
Wireless networking allows devices to connect without physical cables, typically using Wi-Fi. While it improves flexibility and mobility, it introduces significant security risks due to its broadcast nature.
Core Concepts:
Unlike wired networks, wireless signals extend beyond physical boundaries, making them easier to intercept.
Access Points (APs): Devices that connect wireless users to the network
-
Risk:
Unauthorized or misconfigured APs can expose the network
-
SSID (Service Set Identifier):
The network name visible to users
- Control Insight: Hiding SSID provides minimal security—it is not a strong control
-
Wireless LAN (WLAN):
Network formed by wireless devices and access points
-
Modes of Operation:
- Infrastructure Mode: Devices connect through an AP, More secure and manageable
- Ad Hoc Mode: Devices connect directly to each other, No centralized control
- Exam Tip: Ad hoc networks are generally not recommended in enterprises
-
Encryption in Wireless:
- Protects data in transit : without encryption → data can be intercepted easily
-
Authentication Mechanisms:
- Pre-Shared Key (PSK): Shared password
- Risk: Weak passwords compromise entire network
- Enterprise Authentication (802.1X)
- Uses centralized authentication server (e.g., RADIUS)
- Stronger control with: Individual user authentication and Better accountability
- Exam Tip: 802.1X = Best practice for enterprises
- Pre-Shared Key (PSK): Shared password
-
Mobile Device Risks in Wireless Networks
- Lost/stolen devices, Unauthorized access, Malware
- Controls: Mobile Device Management (MDM), Encryption, Remote wipe capability
Wireless Security Protocols
WEP/ WPA / WPA2 / WPA3
| Protocol | Strength |
| WEP | Old and Insecure – Exam Answer: WEP should never be used |
| WPA | Better than WEP but outdated |
| WPA2 | Strong (widely used) |
| WPA3 | Strongest (latest standard) – Exam Insight: If asked for BEST option → WPA3 |
Wireless Security Risks
| Risk | Description | Key Audit Concern | Exam Insight / Tip |
| Rogue Access Points | Unauthorized wireless access points connected to the network | Bypass of security controls and unauthorized network access | Always ensure network monitoring (WIDS/WIPS) and access point detection |
| Evil Twin Attack | Fake access point mimicking a legitimate network | Credential theft and unauthorized access | Strong authentication (802.1X) is more effective than SSID-based trust |
| Eavesdropping | Interception of wireless traffic | Exposure of sensitive data | Use strong encryption (WPA2/WPA3)—encryption is the primary control |
| War Driving | Scanning for vulnerable wireless networks | Identification of weak or unsecured networks | Disable weak configurations and enforce secure wireless setup |
| Denial of Service (DoS) | Flooding network to disrupt services | Loss of availability and service disruption | Implement monitoring and resilience controls (e.g., alerts, redundancy) |
Wireless Security Controls (CISA Revision Table)
| Control | Description | Key Audit Concern | Exam Tip / Insight |
| Strong Encryption (WPA2/WPA3) | Use modern encryption protocols to protect wireless communication | Data exposure if weak or no encryption is used | Always choose WPA3 (best) or WPA2; WEP is never correct in exam |
| Network Segmentation | Separate wireless network from internal/corporate network (e.g., guest Wi-Fi isolation) | Unauthorized access to internal systems | Segmentation is a high-value control—often the BEST answer |
| MAC Address Filtering | Allows only pre-approved devices to connect | Can be bypassed via MAC spoofing | Considered a weak control—never sufficient alone |
| Disable SSID Broadcasting | Hides network name from casual users | Provides minimal security benefit | Security through obscurity—weak control, not a primary defense |
| Power Control | Limits wireless signal range to reduce exposure outside premises | Signal leakage beyond physical boundaries | Useful as a supporting control, not a primary one |
| WIDS (Wireless Intrusion Detection System) | Detects suspicious wireless activities and threats | Threats may go unnoticed if not monitored | Detective control—alerts but does not stop attacks |
| WIPS (Wireless Intrusion Prevention System) | Detects and actively prevents wireless attacks | Without prevention, attacks may succeed | Stronger than WIDS—preventive control preferred in exam |
| Regular Monitoring | Continuous observation of wireless activity to detect rogue APs and anomalies | Delayed detection of attacks | Monitoring is critical—no monitoring = weak control environment |
High-Value Exam Comparisons
| Concept | Key Difference |
| WEP vs WPA2 | Weak vs strong encryption |
| WPA2 vs WPA3 | Strong vs strongest |
| PSK vs 802.1X | Shared password vs centralized authentication |
| WIDS vs WIPS | Detect vs detect + prevent |
| SSID hiding vs encryption | Weak vs strong control |
Data Governance & Database Management
Protection of databases to ensure confidentiality, integrity, and availability of stored data.
Key areas include:
Access Controls: Restrict who can access data and what they can do. Controls include: Role-Based Access Control (RBAC), Least privilege principle
Risk: Excessive privileges → data breaches
Main controls are:
1. Database Authentication and Data Integrity Controls to Ensure data is accurate and not altered improperly.
2. Database Encryption including Data at rest encryption, Transparent Data Encryption (TDE) Difference:
- Encryption at rest → protects stored data
- Encryption in transit → protects moving data
3. Database Activity Monitoring (DAM) to detect unauthorized queries and Logs user actions.
Exam Insight: Monitoring without review = weak control.
4. Backup and Recovery (Database-Specific): controls include Regular backups, Transaction log backups, Point-in-time recovery
5. Database Hardening: controls include: Securing database configurations, Disable default accounts, Remove unnecessary services, Patch vulnerabilities
Audit Focus
- Are privileged users monitored?
- Is sensitive data encrypted?
- Are database logs reviewed?
DBMS Architecture (Exam-Focused Explanation)
What it is
DBMS (Database Management System) architecture defines how a database is structured, accessed, and managed across different layers and components.
For CISA, the emphasis is not on technical design but on:
- Control points
- Data integrity
- Security exposure
- Auditability
Three-Level (ANSI/SPARC) Architecture
View Level |
Control Requirements |
External Level (User View)
|
Data Hiding
Access control principles – Least privilege, Need-to-Know |
Conceptual Level (Logical Structure)
|
Ensures data consistency and integrity
Central point for defining rules (constraints) |
Internal Level (Physical Storage)
|
Impacts performance and availability
Critical for backup and recovery |
Data Independence
| Ability to change one level without affecting others, like Change logical structure without affecting users and Change storage without affecting logical design |
Exam Insight:
Data independence improves flexibility and control stability
DBMS Components
Components |
Features |
Risk and Audit’s Insight |
| Query Processor | Responsible for interpreting and executing SQL statements issued by users or applications. optimizes queries to improve performance by selecting the most efficient access path | SQL injection attacks due to weak input validation can result in unauthorized data access, data leakage, or even complete database compromise.
Auditor ensure the use of parameterized queries, input validation, and secure coding practices. |
| Database Engine | Core component of the database management system (DBMS) that handles data storage, retrieval, and manipulation. It manages how data is physically stored on disk and ensures that queries are executed correctly and efficiently. | Required controls are access controls, data integrity constraints, and security policies (such as role-based access control and encryption mechanisms).
Auditor verify least privilege access is implemented, integrity constraints (e.g., primary/foreign keys) are enforced, and sensitive data is protected through encryption and proper configuration |
| Transaction Manager | Ensures that all database transactions comply with the ACID properties:
o Atomicity (all-or-nothing execution) o Consistency (database remains in a valid state) o Isolation (transactions do not interfere with each other) o Durability (committed transactions are permanently saved) |
Failure in transaction management can lead to data inconsistency, partial updates, or data corruption, especially during system failures or concurrent access scenarios.
Auditor checks for proper implementation of commit/rollback mechanisms, concurrency controls (locking, isolation levels), and reliable backup/recovery processes to ensure durability. |
ACID Properties
| Property | Meaning | Audit Relevance |
| Atomicity | All or nothing | Prevents partial updates |
| Consistency | Valid state maintained | Ensures integrity |
| Isolation | Transactions don’t interfere | Prevents data conflicts |
| Durability | Changes persist | Ensures recovery |
Exam Tip:
If a question mentions data corruption during concurrent access → Isolation issue
Types of DBMS Architecture
| Type | Features | Audit Perspective | Risks |
| Centralized database | Stores all data in a single location, making administration and control relatively straightforward | Simplifies monitoring, access control, and backup management | Introduces a single point of failure, meaning that any disruption (e.g., system crash or attack) can impact the entire database environment. |
| Distributed Database | Spreads data across multiple physical locations. Improves availability and performance | Should specifically focus on controls like data synchronization mechanisms, encryption during transmission, and consistent access policies across all nodes. | Data inconsistency and complex security management |
Client-Server Architecture
In a two-tier architecture, the client directly communicates with the database. While this setup is simple, it exposes the database layer more directly, increasing the risk of unauthorized access and weak security controls, especially if clients are not properly secured.
A three-tier architecture, which includes a client, application server, and database, is the most important from a CISA perspective. The application server acts as an intermediary, enforcing business logic and security controls. This design ensures better segregation of duties, improved access control, and enhanced scalability.
Exam Tip: it is important to remember that three-tier architecture is more secure and better controlled than two-tier architecture.
Data Models
| Model | Features |
| Relational Model | a. Data is organized into tables consisting of rows and columns
b. Most widely used model c. Has ability to enforce data integrity through constraints and relationships d. Reliable and controllable |
| Hierarchical and network models | a. Organize data in tree or graph structures
b. Useful in specific scenarios, but generally less flexible c. Less commonly used |
👉 Exam Tip: Focus primarily on relational databases, as they are most relevant for CISA.
Keys and Relationships (Integrity Focus)
| Primary Key | Uniquely identifies each record within a table, preventing duplication and ensuring entity integrity |
| Foreign Key | Establishes relationships between tables and enforces referential integrity, ensuring that linked data remains consistent |
Exam Insight: When questions focus on data accuracy and integrity, constraints are typically the most relevant control mechanism.
Database Normalization
The process of organizing data aims to reduce redundancy. It Improves integrity and Reduces duplication
Exam Insight:
Normalization → integrity
Denormalization → performance
Logging and Transaction Trails
- Recording database activities (transactions, updates)
- Control Importance: Supports audit trail, Enables recovery
- Exam Tip: No logs = no accountability
Concurrency Control: Managing simultaneous database access
o Issues: Lost updates, Dirty reads
o Control Mechanisms: Locking, Timestamping
o Exam Insight: Concurrency issues → integrity risk
o Database Interfaces and APIs: Ways applications interact with DBMS (ODBC, JDBC)
o Risk: Improper validation → SQL injection
How DBMS Architecture Links to Audit Questions
CISA rarely asks:
❌ “What is ANSI/SPARC?”
Instead, it asks:
✔ “Which control ensures users cannot access underlying data structures?”
→ Answer: External layer / access control
✔ “What ensures transactions are not partially processed?”
→ Answer: Atomicity
✔ “What architecture improves security and segregation?”
→ Answer: Three-tier architecture
High-Value Comparisons (Frequently Tested)
| Concept | Key Difference |
| IDS vs IPS | Detect vs Detect + Prevent |
| Firewall vs IDS | Prevent vs Detect |
| Encryption at rest vs in transit | Stored vs moving data |
| Network segmentation vs firewall | Architecture vs control |
| Monitoring vs logging | Observing vs recording |
Monitoring and Logging
Logging: The process of recording events and activities within systems, applications, databases, and networks.
Examples: User logins/logouts, Configuration changes, Transaction activities, Security events
Monitoring: The process of actively reviewing and analyzing logs and system activities to detect anomalies, incidents, or policy violations.
| Concept | Meaning |
| Logging | Recording events |
| Monitoring | Reviewing and acting on events |
Exam Insight: Logging without monitoring = ineffective control
Objectives of Logging and Monitoring
From an auditor’s perspective, these controls ensure:
- Accountability → Who did what and when
- Traceability → Ability to reconstruct events
- Security detection → Identify unauthorized activities
- Operational visibility → Detect failures and performance issues
- Compliance → Meet regulatory/audit requirements
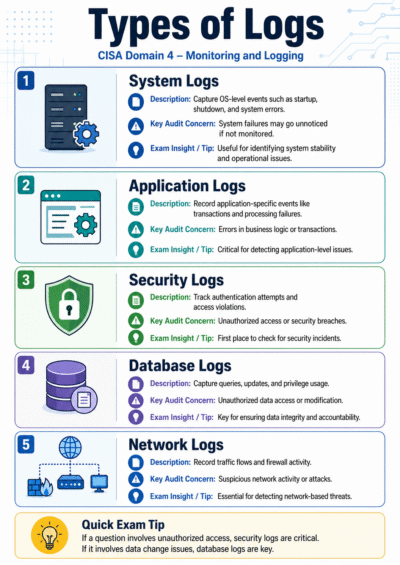
Types of Logs
Log Type |
Description |
Key Audit Concern |
Exam Insight / Tip |
| System Logs | Capture OS-level events such as startup, shutdown, and system errors | System failures may go unnoticed if not monitored | Useful for identifying system stability and operational issues |
| Application Logs | Record application-specific events like transactions and processing failures | Errors in business logic or transactions | Critical for detecting application-level issues |
| Security Logs | Track authentication attempts and access violations | Unauthorized access or security breaches | First place to check for security incidents |
| Database Logs | Capture queries, updates, and privilege usage | Unauthorized data access or modification | Key for ensuring data integrity and accountability |
| Network Logs | Record traffic flows and firewall activity | Suspicious network activity or attacks | Essential for detecting network-based threats |
Exam Tip:
If a question involves unauthorized access, security logs are critical
If data change issue, database logs are key
Key Risks in Logging and Monitoring
| Risk | Description | Impact | Exam Insight / Tip |
| Logs Not Reviewed | Logs are generated but not analyzed | Incidents go undetected | Logging alone is insufficient—monitoring/review is critical |
| Incomplete Logging | Critical events are not captured (e.g., admin activities not logged) | Lack of visibility into important actions | Ensure comprehensive logging, especially for privileged users |
| Log Tampering | Logs can be altered or deleted | Loss of forensic evidence and accountability | Protect logs using access controls and secure storage |
| Lack of Time Synchronization | Systems have inconsistent timestamps | Inability to reconstruct incidents accurately | Use centralized time synchronization (e.g., NTP) |
| Excessive Logging Without Analysis | Large volume of logs with no meaningful review | Important events overlooked | Implement exception-based monitoring |
| No Real-Time Monitoring | Monitoring is delayed or periodic | Slow detection of incidents | Prefer real-time alerts and automated monitoring |
| Lack of Segregation of Duties | Administrators can modify logs | Increased risk of fraud or concealment | Enforce SoD between admin and log management |
| No Retention Policy | Logs are deleted too early | Loss of historical data and audit trail | Define log retention based on compliance and business needs |
Exam Insight:
Most correct answers focus on:
✔ Improving review, protection, or completeness of logs
Key Controls (Auditor’s Interest)
| Control Area | Description | Key Audit Concern | Exam Insight / Tip |
| Log Generation (Completeness) | Capture critical events such as logins (success/failure), privileged activities, system changes, and errors/exceptions | Missing logs reduce visibility into critical activities | Always ensure all critical events—especially admin actions—are logged |
| Log Protection (Integrity) | Restrict access and store logs securely (e.g., write-once media or centralized systems) | Logs can be altered or deleted | Admins should not be able to modify logs—protect integrity |
| Log Review (Most Important) | Regular review of logs (manual or automated), with exception-based reporting | Logs exist but are not analyzed | In many questions, log review is the BEST answer |
| Real-Time Monitoring | Generate alerts for suspicious activities (e.g., failed logins, unauthorized access attempts) | Delayed detection of incidents | Prefer real-time alerts over periodic checks |
| Time Synchronization | Use centralized time source (e.g., NTP) across systems | Inconsistent timestamps hinder investigations | Essential for accurate incident reconstruction |
| Centralized Logging (SIEM) | Aggregate logs from multiple systems into one platform | Fragmented visibility across systems | Enables event correlation and better monitoring |
| Retention & Archiving | Define how long logs are stored based on legal and business needs | Loss of audit trail if logs are deleted early | Retention must align with compliance requirements |
| Segregation of Duties (SoD) | Separate responsibilities for log generation, review, and system administration | Conflict of interest and potential manipulation | Enforce SoD to maintain accountability and integrity |
Audit Focus Areas: An auditor should verify
- Are all critical systems generating logs?
- Are logs protected from unauthorized changes?
- Are logs reviewed regularly?
- Is there real-time alerting?
- Are timestamps synchronized?
- Is there centralized monitoring?
Typical CISA Exam Scenarios
Scenario |
Issue Identified |
Best Answer (Control) |
Exam Insight / Tip |
| Scenario 1 | Logs are generated but not reviewed | Implement regular log review/monitoring. | Logging alone is ineffective—review is critical |
| Scenario 2 | Unauthorized changes occurred but cannot be traced | Improve logging and audit trails | Ensure complete and traceable logging |
| Scenario 3 | Logs exist but timestamps differ | Implement time synchronization | Use centralized time (e.g., NTP) for accurate correlation |
| Scenario 4 | Admin can delete logs | Enforce log protection and segregation of duties | Protect logs and ensure SoD to prevent tampering |
| Scenario 5 | Too many alerts, no action taken | Implement exception-based monitoring | Focus on meaningful alerts, not volume |
How to Think Like a CISA Candidate (CISA Domain 4 exam tips)
When solving questions, always ask:
- Does this control prevent, detect, or correct?
- Is this ensuring availability, integrity, or confidentiality?
- Is the solution proactive or reactive?
- Is there proper segregation of duties?
Final Revision Summary (Must Remember)
- Preventive controls > Detective > Corrective
- Proactive monitoring > Reactive response
- Segregation of Duties is critical everywhere
- Backup ≠ Availability
- Incident ≠ Problem
- Authentication ≠ Authorization
- Change Management governs everything
- Logs must be reviewed, not just stored
FAQs
What is CISA Domain 4?
Why is a CISA Domain 4 revision guide important?
What should be included in CISA Domain 4 study notes?
What are the most important CISA Domain 4 exam tips?
Why is wireless security important in CISA Domain 4?
What is the best wireless security control for the CISA exam?
What is the difference between WIDS and WIPS in wireless security?
What is monitoring and logging in CISA Domain 4?
Why is logging without monitoring a weak control?
What is the difference between logging and monitoring?
How can I prepare for CISA Domain 4 effectively?
https://www.isaca.org/credentialing/cisa



