Introduction
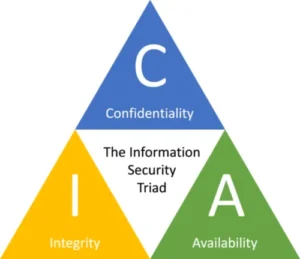
The concepts of CIA Triad, i.e., confidentiality, integrity, and availability, are introduced to all cybersecurity students prior to their first encounter with actual networks, systems and data. You remember the CIA Triad for an exam. You write it on flashcards. Since every CC, CISSP and CISM notes stresses its importance, you find yourself repeating “confidentiality integrity availability” over and over again. But the CIA Triad is not a lesson. It is a battlefield. It is what keeps cloud environments alive. It is what protects data centers from chaos. It is what shields LANs from insider threats and WANs from outages. It is the foundation of every security framework and the first step for anyone searching for cybersecurity.
Why the CIA Triad Still Matters in Modern Cyber Security
Every modern security standard points back to these three pillars:
- Confidentiality. Maintaining legally mandated controls over data access and disclosure, including safeguards for sensitive individual data and proprietary information. A system without confidentiality leaks secrets
- Integrity. Protecting against unauthorized information alteration or deletion, as well as guaranteeing the authenticity and non-repudiation of information. A system without integrity loses truth.
- Availability. Making sure that people can get to and use information reliably and on time. A system without availability cannot function when it is needed.
If you are searching for CIA triad explained for beginners guide or “information security CIA model” that actually sticks, you will see it in ISO 27002, NIST, CIS Controls. Cloud security frameworks, Risk assessments and in every other security architecture map. They all orbit the CIA triad.
How cloud works and why it’s important for modern cybersecurity
The cloud is the engine room of today’s digital world. Instead of running applications on local machines or physical servers in a back office, companies now rely on a global network of remote data centers that deliver computing power on demand. At its core, the cloud is a collection of massive facilities filled with virtualized servers, storage clusters, high-speed networks, distributed databases, container platforms, and hypervisors that carve physical machines into flexible virtual resources. These data centers are tied together with redundant fiber links and backed by layers of automation. The result is a system that lets businesses scale instantly, deploy applications with a click, and recover from failures faster than old environments ever could.
To build a cloud environment, you need infrastructure that is both powerful and resilient. This includes compute servers packed into racks, storage arrays that replicate data across regions, network switches that move traffic with near zero delay, cooling systems that keep everything alive, and highly automated orchestration tools that manage thousands of virtual workloads at once. A cloud environment also depends on identity platforms, monitoring systems, encryption services, private connectivity options, and strict physical security. The cloud works because its providers run this massive, distributed architecture so customers do not have to.
Most people interact with the cloud through its service models. Infrastructure as a Service gives you virtual machines, networks, and storage. Platform as a Service provides ready-to-use environments for building applications without managing servers. Software as a Service delivers complete products like email, CRM tools, and collaboration platforms. These layers allow startups to launch globally, enterprises to migrate entire data centers, and developers to build without worrying about hardware.
The biggest players in the market are Amazon Web Services, Microsoft Azure, and Google Cloud Platform. Together, they run the majority of the world’s cloud workloads. Other contenders include Alibaba Cloud, Oracle Cloud, IBM Cloud, DigitalOcean, and niche providers that focus on specific industries.
As organizations move deeper into the cloud, the demand for cloud cybersecurity grows at record speed. Every industry now needs people who understand cloud identity, encryption, shared responsibility models, zero trust architecture, network segmentation, incident response, and compliance, i.e., the cloud CIA triad. Cloud breaches often happen not because the providers fail, but because customers misconfigure access, leave storage exposed, or lack proper monitoring. This has created a massive opportunity for professionals who can protect cloud workloads and design secure architectures that meet business and regulatory requirements.
Cloud Confidentiality Controls
Cloud confidentiality controls ensure only authorized people, systems, or services can access sensitive data. They rely on encryption, IAM, private networking, secret management, monitoring, and automated guardrails.
These are the frontline protections for cloud privacy, compliance, and secure architecture. Here are common confidentiality controls across IT environments:
-
Encryption at Rest
Cloud providers encrypt stored data using keys managed by the service or by you (KMS, customer-managed keys, or HSMs).
Examples:
- AWS S3 encryption
- Azure Storage Service Encryption
- Google CMEK/HSM
Why it matters: if someone gets access to the storage layer, they cannot read the data.
-
Encryption in Transit
TLS, HTTPS, and VPN tunnels ensure no one can eavesdrop or intercept data moving across networks.
Examples:
- HTTPS load balancers
- TLS between microservices
- IPSec tunnels between cloud and on-prem
Why it matters: protects data as it moves, especially across public networks.
-
Identity and Access Management (IAM)
IAM is one of the strongest confidentiality protections in the cloud because it controls who can access what.
Key IAM controls:
- role-based access control (RBAC)
- least privilege access
- temporary credentials
- access policies per resource
- identity federation (SSO)
Why it matters: prevents unauthorized users or services from accessing sensitive resources.
-
Multi-Factor Authentication (MFA)
Admins, engineers, and console users should always authenticate with MFA.
Examples:
- AWS MFA for root and IAM users
- Azure AD MFA
- Google Cloud Identity MFA
Why it matters: It stops attackers even if they steal a password.
-
Network Segmentation
Cloud networks isolate sensitive systems using:
- VPCs
- private subnets
- security groups
- network ACLs
- zero-trust network design
Why it matters: It keeps sensitive data away from public exposure.
-
Private Endpoints and Private Connectivity
Services like S3, Azure Storage, or databases can be accessed privately through:
- VPC endpoints
- PrivateLink
- Azure Private Endpoint
- Google Private Service Connect
Why it matters: sensitive data never touches the public internet.
-
Secret Management
Cloud platforms provide secure storage for secrets, passwords, and tokens.
Examples:
- AWS Secrets Manager
- Azure Key Vault
- GCP Secret Manager
Why it matters: removes hardcoded secrets from code and prevents accidental exposure.
-
Data Masking and Tokenization
Used to hide or tokenize sensitive fields while preserving functionality.
Examples:
- tokenizing credit cards
- masking PII in analytics databases
Why it matters: reduces exposure in development or analytics environments.
-
Logging and Access Monitoring
To protect confidentiality, you must know who accessed what.
Tools:
- AWS CloudTrail
- Azure Monitor
- GCP Cloud Audit Logs
Why it matters: detects unauthorized access attempts and suspicious behaviors.
-
Configuration Policies and Guardrails
Automated policies prevent exposure before it happens.
Examples:
- AWS Config rules
- Azure Policy
- GCP Organization Policies
These can block:
- public storage buckets
- open security groups
- weak encryption settings
Why it matters: stops misconfigurations that cause most cloud confidentiality breaches.
-
Data Loss Prevention (DLP)
Cloud-native or third-party DLP tools inspect data movement to prevent leaks.
Examples:
- Google DLP API
- Microsoft Purview DLP
- CASB solutions
Why it matters: identifies sensitive data and stops it from leaving the environment.
-
Client-Side Encryption (High Security)
The strongest confidentiality measure of all: encrypt before sending data to the cloud.
Why it matters: cloud providers see ciphertext, not plaintext. Only the customer controls keys.
Cloud Integrity Controls
Integrity protects the accuracy of information. No silent edits. No hidden manipulation. No tampered logs. If confidentiality protects secrecy, integrity protects truth.
This is one of the least understood parts of the CIA triad for beginners and one of the most tested topics in Cyber security exams i.e. integrity in information systems
-
Versioning
Cloud storage systems like AWS S3, Azure Blob, and Google Cloud Storage can keep older versions of files. If someone modifies or deletes something by mistake or through an attack, you can roll back to a clean version.
Why it matters: prevents silent tampering and accidental edits.
-
Immutable Backups
Immutable backups freeze data so it cannot be changed, overwritten, or deleted for a set period.
Ransomware cannot encrypt them. Admins cannot modify them.
Why it matters: protects against corruption, insider threats, and ransomware.
-
Checksums and Hashing
Cloud services calculate hashes of files during upload and download. If the hash changes, something tampered with the data.
Why it matters: ensures the data you receive is the exact data you sent.
-
Digital Signatures
Used for objects, documents, code, APIs, and system updates. If a signature does not match, you know the content has been altered.
Why it matters: stops unauthorized changes and proves who signed what.
-
Audit Logging
Cloud providers generate detailed logs for access, changes, and actions. This includes logs like AWS CloudTrail, Azure Activity Logs, and Google Cloud Audit Logs.
Why it matters: you can trace who did what, when, and where. If someone edits data, you can confirm the source.
-
Database Integrity Controls
Cloud databases include built-in controls such as:
- point-in-time recovery
- transaction logs
- write-ahead logging
- integrity constraints and checks
Why it matters: protects against corruption, injection attacks, and unauthorized changes.
-
Object Locking
Services like Amazon S3 Object Lock prevent deletion or modification for a chosen retention period.
Why it matters: critical for compliance and fraud prevention.
-
Change Management and Approval Workflows
Cloud platforms support automated pipelines where all changes require approval or review. Tools like AWS Config and Azure Policy can detect unauthorized modifications.
Why it matters: stops unapproved edits and enforces accountability.
-
Integrity Monitoring Tools
Solutions like AWS GuardDuty, Azure Security Center, and Cloud Monitoring tools watch for:
- unusual changes
- unexpected configurations
- unauthorized data access
- risky edits in real time
Why it matters: alerts you instantly when something is tampered with.
-
End-to-End Encryption Validation
Some systems validate encrypted data along the path to ensure it is not modified in transit.
Why it matters: protects data consistency between services, regions, and customers.
Cloud Availability Controls
Availability ensures systems stay up and reachable. It is the least glamorous but often the deadliest pillar to lose. Search availability in cyber security examples and you will find outage after outage.
Availability collapses in seconds when redundancy fails. Therefore availibility is the most important pillar of CIA Triad
-
Multi-AZ (Availability Zone) Deployment
Apps and databases are deployed across multiple availability zones within the same region.
Examples:
- AWS Multi-AZ RDS
- Azure Availability Zones
- Google Cloud Multi-Zone clusters
Why it matters: If one zone fails due to power loss or hardware issues, the app continues running in another zone.
-
Multi-Region Redundancy
Critical systems run in two or more regions.
Used for:
- disaster recovery
- global applications
- high uptime SLAs
Why it matters: Regional outages do happen. Multi-region design ensures global availability.
-
Auto Scaling
Automatic scaling of compute resources based on traffic or workload.
Examples:
- AWS Auto Scaling Groups
- Azure VM Scale Sets
- GCP Instance Groups
Why it matters: Prevents downtime during traffic spikes or unexpected demand.
-
Load Balancing
Distributes traffic across healthy instances.
Types:
- layer 4 and layer 7 load balancers
- global load balancers
- internal load balancers
Examples:
- AWS ELB/ALB/NLB
- Azure Load Balancer
- Google Cloud Load Balancing
Why it matters: No single server becomes a bottleneck or point of failure.
-
Health Checks and Automatic Failover
Cloud systems constantly check instance health and reroute traffic automatically.
Examples:
- RDS failover
- GCP health checks
- Azure Traffic Manager probes
Why it matters: If a node fails, traffic moves instantly to healthy resources.
-
Redundant Storage and Replication
Cloud storage automatically replicates data:
- within availability zones
- across zones
- optionally across regions
Examples:
- S3 cross-region replication
- Azure GRS
- Google Cloud Multi-Region Storage
Why it matters: Prevents data loss and enables fast failover.
-
Backup and Restore (Disaster Recovery Plans)
Taking frequent snapshots and full backups of:
- databases
- VMs
- storage buckets
- key services
Why it matters: Availability includes the ability to recover quickly and cleanly.
-
Content Delivery Networks (CDNs)
CDNs like CloudFront, Azure CDN, and Cloud CDN cache static assets globally.
Why it matters: Your application remains fast and reachable even if your core region is overloaded.
-
Distributed DNS
Using cloud-native DNS with global redundancy.
Examples:
- Route 53
- Azure DNS
- Google Cloud DNS
Why it matters: DNS is a high-value target. Redundant DNS keeps your site reachable during DDoS or network failures.
-
DDoS Protection
Cloud providers offer built-in and advanced DDoS filtering.
Examples:
- AWS Shield
- Azure DDoS Protection
- Google Cloud Armor
Why it matters: Prevents attackers from knocking your services offline.
-
Serverless Architectures
Services like AWS Lambda scale instantly and remove single-server failure risks.
Why it matters: Serverless functions inherit cloud resilience, automatically scaling and self-healing.
-
High Availability Databases
Cloud databases include built-in HA features:
- failover replicas
- read replicas
- synchronous replication
- automatic patching
Examples:
- DynamoDB global tables
- Azure Cosmos DB multi-region writes
- Cloud SQL HA configurations
Why it matters: Databases are often the hardest part of availability.
-
Infrastructure as Code (IaC) for Fast Recovery
Tools like Terraform and CloudFormation recreate infrastructure quickly.
Why it matters: If a region goes down, you can redeploy a full environment in minutes.
- Monitoring and Alerting
Cloud-native monitoring tools ensure issues are caught early.
Examples:
- CloudWatch
- Azure Monitor
- Google Cloud Operations
Why it matters: You cannot maintain availability without visibility.
-
Chaos Engineering
Teams simulate failures intentionally to test resilience.
Tools:
- AWS Fault Injection Simulator
- Chaos Monkey
Why it matters:
You discover weaknesses before real failures happen.
In summary Cloud availability controls make sure your systems stay online even when:
- servers fail
- regions go dark
- traffic spikes
- networks break
- attackers launch DDoS attacks
- workloads shift unexpectedly
Availability is not luck. It is architecture
Conclusion
For students preparing for roles in cyber security, the cloud offers a wider scope than traditional data centers ever did. The field needs architects who can design resilient systems, analysts who detect attacks across hybrid environments, engineers who automate security controls, and specialists who understand how confidentiality, integrity, and availability (i.e., the CIA triad) work in distributed systems.
The cloud is no longer optional. It is the environment where modern security skills are built, tested, and needed every day. Security skills are encompassed within the CIA Triad.
The CIA triad is a foundational information-security model consisting of confidentiality, integrity, and availability; in cloud environments it is used to evaluate access control, data protection, and service resilience.
For further study please follow
https://www.nccoe.nist.gov/publication/1800-26/VolA/index.html