The Top 6 Cyber Security Specialist Jobs in 2026
November 20, 2025
No Comments
Cybersecurity is no longer merely a buzzword, it has become a prominent career pathway for Cyber Security Specialist jobs. Cybersecurity has evolved from a niche ...
Read More →
Cryptography is Ready — The Internet is Not: Challenges for Companies in the Post-Quantum Transition
October 6, 2025
No Comments
Post Quantum Cryptography Companies are facing challenges in safeguarding data against future quantum attacks while maintaining compatibility. Today's public-key encryption faces a real long-term threat ...
Read More →
Cost vs. Impact: Rethinking How We Classify Assets
October 2, 2025
No Comments
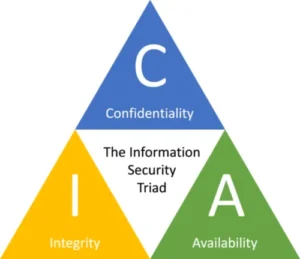
Introduction The CIA triad, i.e., confidentiality, integrity, and availability, is the foundation of cybersecurity for asset classification. However, many businesses still view classification as a compliance ...
Read More →
From Wasted Investments to Real Protection: Why Context Matters in ISMS
September 22, 2025
No Comments
ISMS context is the foundation of a successful information security program. When organizations begin the process of building an Information Security Management System (ISMS), they ...
Read More →
Trending Topics
A Phishing Email Protection in 2025: Survival Guide
October 12, 2025
No Comments
A phishing email protection in 2025 is a major challenge. One rushed click, One fake "verify now" link: Suddenly, your mailbox is compromised, followed by ...
Read More →
9 Shocking Cyber Security Case Studies You Need to Know
September 8, 2025
No Comments
This article reviews several high-profile cyber attacks, providing case study insights into incidents like the Sony Pictures hack and the Stuxnet worm. It examines how ...
Read More →
Cyber Threats
September 7, 2025
No Comments
Cyber threats refer to malicious activities or actions that aim to compromise the confidentiality, integrity, or availability of digital information, systems, or networks
Read More →
The Inside Look at a Phishing Attack: How Hackers Trick You and How to Protect Yourself
August 30, 2025
No Comments
Phishing attacks are one of the most common ways hackers trick people into giving up passwords and personal data. In this step-by-step guide, you’ll learn ...
Read More →
AI vs AI: The Battle between Cyber Defenders and Attackers
September 2, 2025
AI vs AI in cybersecurity is becoming the ultimate battlefield. Imagine checking your email and seeing a message from the boss urging you to send ...
Zero-Day AI Attacks: What Makes This Different (and Urgent)
September 24, 2025
Zero-Day AI attacks don’t target just code — they exploit models, prompts, and data. From ShadowLeak to prompt injection, here’s why AI threats are different ...
When the Alarm Lies or Stays Silent: How False Positives and Negatives Weaken SOC Effectiveness
September 27, 2025
False positives in SOC, like their counterpart, false negatives, are among the most critical issues in modern cyber protection. Security Information and Event Management (SIEM) ...
From Frameworks to Action: How NIST’s COSAIS Will Protect AI Models
October 4, 2025
While artificial intelligence (AI) has transformative possibilities, it also poses novel cybersecurity threats that conventional security measures might not be able to adequately counter. The ...

Subscribe To Our Newsletter
Get unlimited access to Executive Insight and stay ahead of the curve.
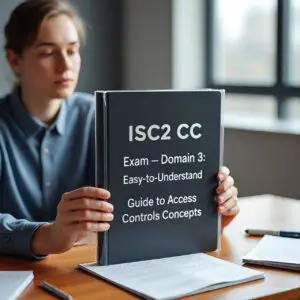
ISC2 CC Exam– Domain 3: Access Controls Concepts : Best Easy Guide
November 23, 2025
No Comments
In this comprehensive guide, we'll break down everything you need to know about physical and logical access controls, from the fences around data centers and ...
Read More →
The CIA Triad in Cloud Security: 2025 Professional Guide for Students and Cybersecurity Practitioners
November 19, 2025
No Comments
The concepts of CIA Triad, i.e., confidentiality, integrity, and availability, are introduced to all cyber security students prior to their first encounter with actual networks, ...
Read More →
Control Self Assessment (CSA)- 2025 Guide: Building Executive Confidence in Information Security Governance
November 15, 2025
No Comments
Control Self Assessment (CSA), a governance tool that enables process owners to regularly assess and enhance their own control environment, is being used by top ...
Read More →
ISC 2 Certified in Cybersecurity CC – Domain 2: Business Continuity (BC), Disaster Recovery (DR) & Incident Response Concepts
November 10, 2025
No Comments
The real test of an organization is not how well it functions in normal circumstances, but rather how it handles disasters and system failures. This ...
Read More →
Certified in Cybersecurity Certification Exam, Domain-1 “Security Principles”
November 3, 2025
No Comments
ISC2 Certified in Cybersecurity (CC) certification is designed for people who are new to the field. This was done because more and more people are ...
Read More →
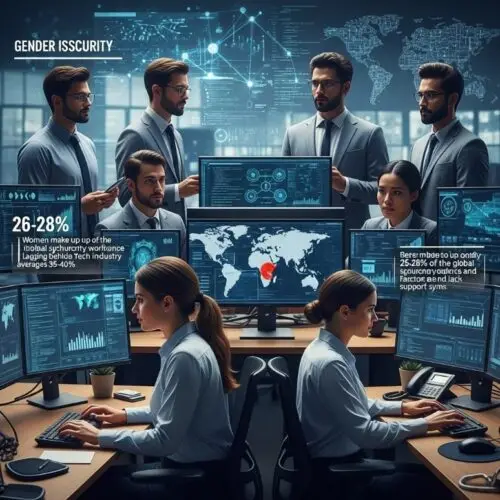
Bridging the Gender Gap in Cybersecurity: Challenges & Opportunities
October 26, 2025
No Comments
The gender gap in cybersecurity remains one of the most persistent challenges in the digital era. Despite significant development and great demand for talent, there ...
Read More →